Why is it Important for Fintech Apps to Have Stronger Authentication Than Ever Before?
Here are some reasons that make Fintech app security stringent when using it in FlutterFlow.Skyrocketing Cyber Threats
Financial apps are the primary targets for hackers. As discussed in the introduction, Fintech is prone to more online attacks than any other industry. Online intruders utilize API breaches, credential stuffing, and phishing attacks to compromise vulnerable, secure login FlutterFlow systems.If you do not effectively utilize behavioral monitoring and multi-factor authentication (MFA), your Fintech app becomes a ticking time bomb that can explode at any time!Stringent Regulatory Requirements
When you adhere to GDPR, PCI DSS, and PSD2, they do not merely suggest that you have strong authentication; they mandate it. If you do not comply with these regulations, you can be fined a maximum of 4% of your global revenue. This is where Firebase authentication of FlutterFlow can come in handy. However, you must prioritize configuring it for Strong Customer Authentication (SCA) to stay legally compliant.User Trust is Fragile
A single online breach headline can erase years of brand loyalty. As per a survey by Qualitest, 88% of app users will stop using their apps if they find a security breach. However, with the help of a fintech app security strategy, you can keep the fintech app technically sound and help retain customers who trust you with their life savings.Mobile-First Perils
Fake Wi-Fi hotspots, screen mirroring attacks, and lost phones can make mobile finance apps vulnerable to online fraud. Since FlutterFlow Firebase authentication is compatible with biometric logins like Face ID and fingerprints, you can counter this situation, albeit only if you execute them with finesse.Real Financial Consequences
Weak authentication can lead to lawsuits, chargebacks, and, in the worst-case scenario, fraudulent transactions. A prime example is Home Depot. Hackers compromised the self-checkout point-of-sale system of the company and infected devices with personal information-skimming malware. This cyberattack proved very costly for the company as it had to pay a hefty fine in excess of $200 million.Future-Proofing
Quantum computing and AI-powered deepfakes have the potential to break today's passwords. This is where adaptive measures are required in Fintech app security, including:- Decentralized identity, like blockchain-based logins
- Behavioral biometrics, like how users swipe/type
Ever-Evolving Compliance Landscape
FedNow and Open Banking are rewriting the rules. Here, a special mention has to be made for CBDCs. However, what is compliant today may not be in the future. This is where it becomes essential to get regular audits done by a top FlutterFlow agency to keep you one step ahead of your competitors.Brand Reputation on the Line
Equifax paid an exorbitant fine of $1.4 billion for a 2017 breach that resulted in open access to the addresses, social security numbers, driving licenses, and even birth dates of its 143 million consumers. Fintechs cannot recover from such reputational damage.Now that you understand the importance of stronger authentication in Fintech apps, we will examine the core authentication methods available on the FlutterFlow platform in the next section.Core Authentication Methods in FlutterFlow
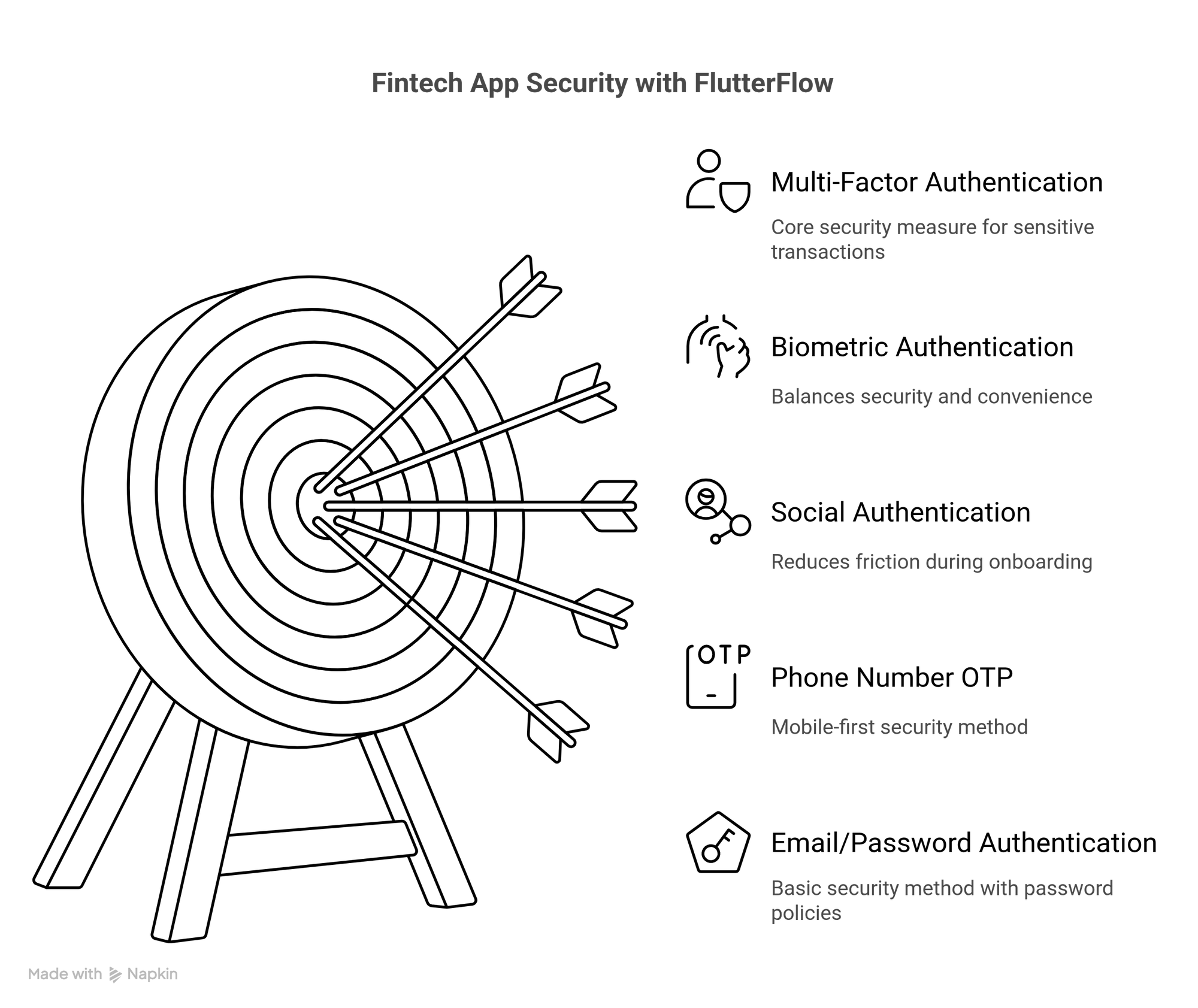
Email/Password Authentication
This is a commonly used method where Firebase automatically manages secure password hashing and storage. But fintech apps must enforce stringent password policies and scrutinize for credential stuffing attacks.Phone Number OTP Verification
This is a specifically valuable authentication method for mobile-first financial services, wherein you use Firebase's SMS delivery system. Although it is user-friendly, it is crucial to execute additional security measures to protect your Fintech app from SIM-swapping fraud, which has become prevalent in today’s time to carry out financial attacks.Social Authentication Providers (Google and Apple sign-in alternatives)
Google and Apple sign-ins can reduce friction levels while onboarding. These methods are a perfect fit for fintech apps that prefer user growth. Financial apps should meticulously manage the requested permissions and contemplate making MFA mandatory after initial social login.Firebase Authentication Integration
The Firebase authentication integration in FlutterFlow acts as the pillar on which all these methods can be implemented effectively by providing session handling and secure token management. With this native integration, the development process becomes simpler, and at the same time, you can maintain enterprise-grade security measures that fintech apps desperately need.Multi-Factor Authentication Requirements
Financial applications must best use multi-factor authentication because it is legally required. Executing MFA through FlutterFlow primarily requires integrating SMS verification with authenticator apps or biometric checks, which is critical for sensitive transactions.Biometric Authentication Alternatives
Features such as Face ID and fingerprint scanning perfectly balance security and convenience for mobile banking applications. Such methods drastically reduce friction while maintaining high-security protocols, although they should always integrate fallback alternatives.Read Also : A Step-by-Step Guide to Secure Authentication Setup for FlutterFlow Fintech Apps
Anonymous Authentication (Comes in handy for trial experiences prior to KYC verification)
This authentication method provides a handy middle ground for fintech apps that wish to provide trial experiences before comprehensive KYC verification. With this authentication method, users can effortlessly explore basic features while maintaining a clear-cut path to get complete account verification as per their requirements for financial transactions.When you, as Fintech FlutterFlow developers, are executing these methods, prioritize regulatory compliance like PSD2’s SCA requirements and contemplate consulting with FlutterFlow security experts to ensure all authentication layers adhere to financial industry standards. With the right combination of these methods, you can create an immaculate yet ultra-secure UX that shields customer data and their business.
Best Practices for Secure Fintech Authentication
Here are some best practices for Fintech app security using FlutterFlow.Enforce Strong Password Policies
Ensure your passwords are a bare minimum of 12 characters long and contain the right mixture of uppercase, lowercase, numbers, and special characters. Execute automatic checks if you locate a password database breach to prevent password reuse from occurring. Using the Firebase authentication in FlutterFlow makes it easier to gain built-in enforcement capabilities. However, for fintech applications, you should integrate extra layers of security, such as periodic mandatory resets.Mandate Multi-Factor Authentication (MFA)
Make MFA authentication mandatory for all user accounts. You can use a combination of a minimum of two-factor authentication, such as possession, email OTP, and SMS, along with inherence, like biometric authentication.If you are dealing with a risky action like wire transfers, integrate an extra authentication step where it is mandatory to have an additional verification. Firebase integration of FlutterFlow is compatible with flexible MFA implementation, which can be personalized according to different risk levels.
Secure Session Management
Execute short session timeouts, such as 15 to 30 minutes of inactivity and automatic logout across devices when a password changes. Make the best use of refresh tokens with stringent expiration policies and ensure all sessions are properly invalidated during logout. Financial applications must maintain comprehensive session logs for audit purposes.Protect Against Brute-Force Attacks
It is imperative that you restrict the hourly deployment rate to 3 to 5 attempts and execute progressive delays between attempts. Including CAPTCHA or behavioral analysis is recommended to ensure that you are dealing with humans and not AI bots. The Firebase Authentication in FlutterFlow allows for certain built-in protections. However, you must integrate extra monitoring for suspicious patterns when discussing fintech apps.Utilize Biometrics for High-Value Transactions
Fingerprint and facial recognition patterns prove to be impeccable yet highly secure authentication, specifically when you are going to take sensitive actions. Execute biometrics as part of MFA flows. This will ensure cryptographic verification locally on your device. Always have a backup security plan ready when using traditional MFA methods for accessibility.Encrypt Data End-to-End
You must ensure that all authentication data is encrypted both in transit (TLS 1.3) and at rest (AES-256). Never store plaintext credentials or even sensitive tokens. The Firebase integration in FlutterFlow manages such functionality automatically, but you must verify encryption practices beforehand for any custom authentication logic.Regular Security Audits and Updates
Perform quarterly penetration tests concentrating on authentication flows. Dependencies like FlutterFlow plugins and Firebase SDK need to be thoroughly observed for vulnerabilities, and then you can apply real-time patches to address them effectively. If you are developing fintech apps, consider opting for round-the-clock security monitoring solutions.User Education and Transparency
Thoroughly explain security measures to users. They should also be provided with guidelines that help them discover phishing attempts. You can ask them to send real-time notifications if they encounter suspicious activity, like new logins and password changes. Transparent communication can help you develop trust. This will go a long way in improving the overall security conditions for your fintech app.Executing these practices effectively often requires expertise. As a Fintech startup, you can partner with a FlutterFlow development company specializing in financial applications to ensure your authentication adheres to security requirements and compliance protocols.
Fortify Your Fintech App from Day One
Discover how to build airtight authentication in FlutterFlow using Firebase and best security practices.

Step-by-Step Guide to Implementing Multi-Factor Authentication in FlutterFlow for Finance Applications
Multi-factor authentication (MFA) is an unassailable security requirement for fintech apps that manage sensitive transactions. Here are the steps to help you implement FlutterFlow MFA effectively while complying with financial regulations like GDPR and PSD2 SCA.Set up Firebase Authentication in FlutterFlow
Before enabling MFA, ensure Firebase authentication is adequately configured in your FlutterFlow project by following these steps:- Visit Firebase Console -> Authentication -> Sign-in method
- Enable Email/Password, Phone, or Social Providers as your core authentication methods.
Enable Multi-Factor Authentication (MFA) in the Firebase Console
Firebase is compatible with SMS OTP and TOTP (Time-Based OTP) for MFA. This is how you can enable it:- Visit Firebase Console -> Authentication -> Multi-factor authentication
- Enable SMS-based MFA for phone verification or TOTP for authenticator apps.
Choose MFA Methods (SMS, Email OTP, Authenticator Apps)
Every action will require a different level of security.- Low Risk (Login) needs SMS or email OTP.
- High Risk (Profile changes and payments) need push notifications or TOTP (Google Authenticator.
const admin = require('firebase-admin');
admin.auth().generateSignInWithEmailLink(email, actionCodeSettings);Configure SMS OTP with a Dependable Provider (Firebase Phone Authentication, Twilio)
Firebase phone authentication is good; however, for high-volume fintech applications, use Twilio for better deliverability. You can configure it by following these steps:- Go to Firebase and enable Phone Authentication
- For Twilio, integrate through Firebase Cloud Functions
Integrate Time-Based OTP (TOTP) for Authentication Apps (Google Authenticator, Authy)
Time-based OTP (TOTP), like Google Authenticator and Authy, has been proclaimed more secure than SMS. Here is how you can integrate it:- Use Firebase’s firebase. Auth.TOTPMultiFactorGenerator
- Display a QR code for users to scan by using this JavaScript:
Personalize MFA Triggers for Dicey Actions (Payments, Profile Changes)
Fintech apps require step-up authentication for:- Large money transfers
- Password/email changes
- New device logins
if (transactionAmount > 1000) {
requireStepUpAuth();
}Implement Fallback Methods for Failed MFA Attempts
In case an SMS fails or the user loses their authenticator, you can ask them to provide the following:- Backup email verification
- Security questions (for low-risk applications)
- Customer support verification (for high-security applications)
Test MFA Flows Comprehensively (Success & Failure Scenarios)
Here, the success path will involve users completing the MFA without hassle. While the failure paths will involve:- Wrong OTP entered
- SMS not delivered
- Authenticator app mismatch
Monitor MFA Logs for Suspicious Activity
- Use the lethal combination of Firebase Analytics and BigQuery to track:
- Failed MFA attempts
- Unusual locations/devices
- Set up alerts for brute-force attacks by using this SQL code in BigQuery:
SELECT * FROM `project.dataset.auth_events`
WHERE event_type = "mfa_failure"
LIMIT 100;
Comply With Financial Regulations (PSD2 SCA, GDPR, Local Laws)
- PSD2 SCA (EU) requires a minimum of two authentication factors for payments.
- GDPR mandates secure storage of authentication data.
- Certain countries' local laws ban SMS OTP, such as India's OTP delay rules.
Advanced Security Measures for Fintech Apps
Here are some advanced security measures for Fintech apps.Behavioral Anomaly Detection
It helps to monitor user interaction patterns like typing speed and transaction times to flag suspicious behavior. You can execute this by using the Python Pseudocode:if current_user.behavior_deviation > threshold:
trigger_step_up_authentication() Device Fingerprinting
This security method creates an exclusive device ID based on hardware/software attributes like OS version, GPU specs, and installed fonts. Here is an example of its JavaScript:const deviceId = generateFingerprint([
'screenResolution',
'timezone',
'webGLRenderer'
]); AI-Powered Fraud Prevention
It utilizes ML models to scrutinize transaction patterns to ascertain anomalies like sudden large withdrawals. Here are some tools that can help you with such a security measure:- TensorFlow Fraud Detection
- AWS Fraud Detector
Dynamic Risk-Based Authentication
This security method adjusts authentication stringency on the basis of real-time risk factors:- The new device will need MFA
- Unusual locations will require a block and alert
if (transactionRisk > 70) {
enforceBiometricReauth();
} Secure Key Management
This security method stores encryption keys in Hardware Security Modules (HSMs) or AWS KMS rather than code/config files. This type of security is crucial for:- PCI DSS compliance
- Preventing API key leaks
Real-Time Threat Intelligence Feeds
This security methodology integrates blocklists of known malicious IPs, compromised credentials, and Tor nodes. Here is a Cloudflare bash code example:Curl -X GET "https://api.cloudflare.com/client/v4/ips"Jailbreak/Root Detection
It blocks access from compromised devices where security checks can be bypassed. Here is an Android Code Snippet of the JavaScript:if (Superuser.isRooted()) {
showSecurityAlertAndLogout();
}Secure Offline Mode Protections
This security method ensures cached data remains encrypted (AES-256) in case the device loses connectivity. Here is the Flutter implementation of Dart code:await FlutterSecureStorage.write(key: 'token', value: encryptedToken);Automated Security Response Playbooks
This security method takes predefined action for threats like:Brute-force attack -> IP ban and admin alertData breach -> Force password resetHere’s a Node.js JavaScript:securityEvents.on('brute_force', (ip) => {
blockIP(ip);
notifyAdmin(`Attack from ${ip}`);
}); Decentralized Identity Verification
It uses blockchain-based Decentralized Identifiers (DID) to tamper-proof user authentication. Here are some emerging standards:- W3C Verifiable Credentials
- Sovrin Network
Common FlutterFlow Authentication Pitfalls & How to Avoid Them
Here are some common FlutterFlow authentication pitfalls and how to avoid them in the best possible way.Hardcoded API Keys in Frontend Code
The risk of this pitfall is that it can expose sensitive keys to attackers..How to Deal with this Limitation:- Make effective use of Firebase Environment Config or .env files.
- If you wish to use backend services, make the best use of Google Cloud Secret Manager.
Poor Error Messages Exposing System Details
Hackers can exploit verbose errors like - No user found with this email.How to Deal with this Limitation: Return generic responses using this Dart code:throw FirebaseAuthException('auth/invalid-credential', 'Invalid credentials');Ignoring Session Timeouts for Financial Apps
This can result in unlimited sessions, which invites hijacking.How to Deal with this Limitation:- Set Firebase ID token expiration to 15-30 minutes.
- Force re-auth for sensitive actions like transfers and KYC changes.
Skipping Rate Limiting on Login Attempts
This can put you at risk of brute-force attacks that can result in the compromise of user accounts.How to Deal with this Limitation:- Effectively employ the rate-limiting feature of Firebase using this JavaScript code:
- Integrate CAPTCHA after three failed attempts.
Overlooking MFA for High-Risk Transactions
This authentication pitfall can lead to unauthorized fund transfers.How to Deal with this Limitation:- Trigger step-up MFA through Firebase’s multiFactor(). Enroll (). Trigger step-up MFA through Firebase’s multiFactor(). Enroll ().
- Make use of TOTP (Google Authenticator) to increase the security level.
Utilizing Weak Password Policies
This makes it easy for intruders to guess the passwords.How to Deal with this Limitation: Enforce this JSON code through Firebase rules:"passwordPolicy": {
"minLength": 12,
"requireLowercase": true,
"requireUppercase": true
} Failing to Monitor Suspicious Logins
It can cause delayed breach detection.How to Deal with this Limitation: Integrate the combination of Firebase Analytics and BigQuery using this SQL code:SELECT * FROM auth_events WHERE login_country != user_country;Not Testing Auth Flows on Real Devices
This can put your Fintech app at risk of getting platform-specific bugs like iOS keychain failures.How to Deal with this Limitation: - Test on physical devices with tools like Firebase Test Lab.
Forgetting to Plan for Auth State Changes
This can make users stay logged in after token revocation.How to Deal with this Limitation: Listen to auth state changes by using this Dart code:FirebaseAuth.instance.authStateChanges().listen((User? user) { ... });Assuming Firebase Auth Alone is Enough
This problem can make you miss out on advanced threats like behavioral fraud.How to Deal with this Limitation: Layer with AI fraud detection like AWS Fraud Detector.Even though FlutterFlow simplifies authentication, fintech applications require proactive hardening. If you are looking for complex implementations, consider affiliating with a top FlutterFlow development agency that specializes in financial security.How Does Third Rock Techkno’s Prowess Help Build Secure Authentication in FlutterFlow for Your Fintech Apps?
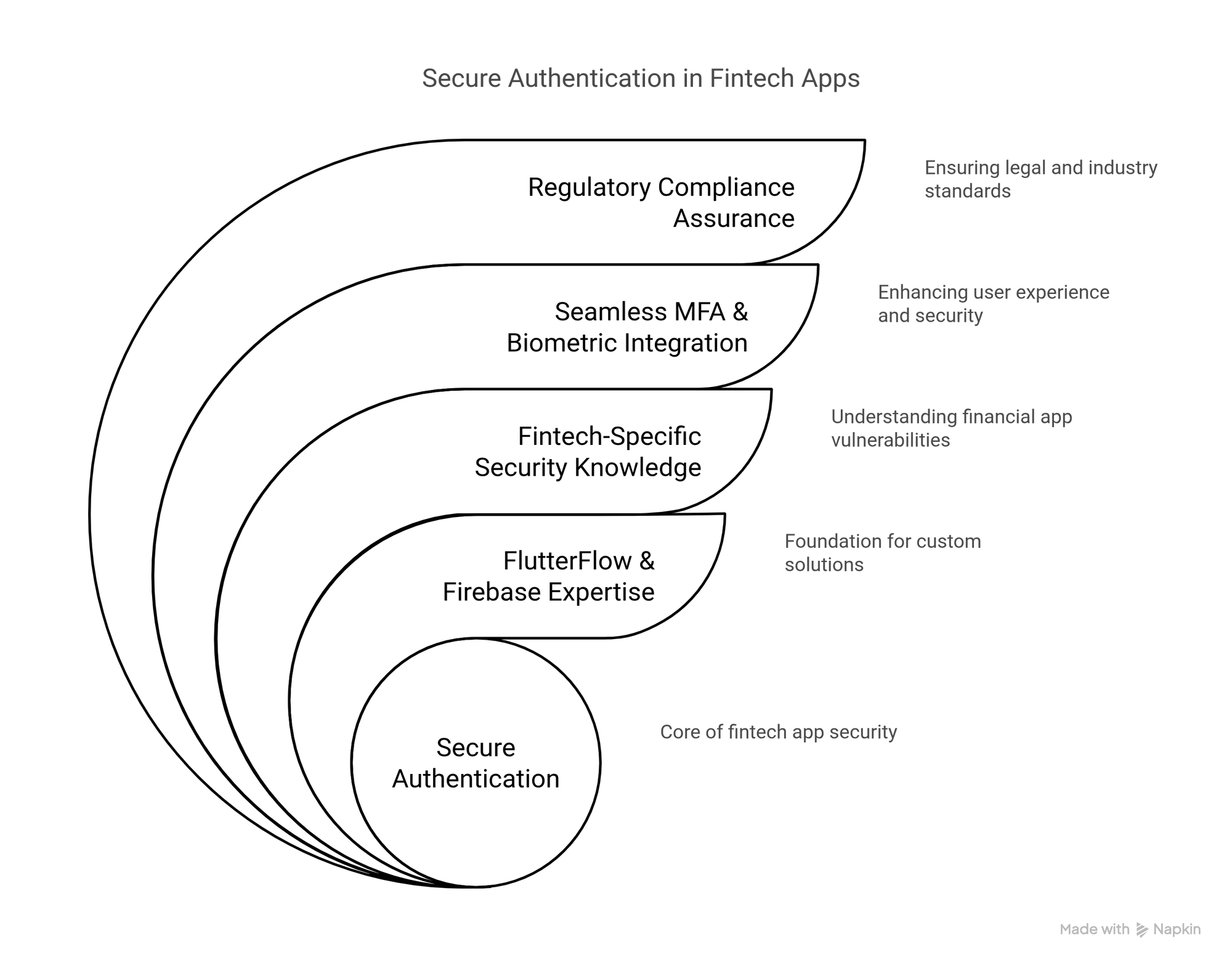
Deep FlutterFlow and Firebase Expertise
We at Third Rock Techkno have a talented team of FlutterFlow developers who push their limits when it comes to fintech security by providing custom Firebase authentication workflows specifically created for financial applications. They also use advanced implementations like JWT validation, real-time threat logging, and session hijacking prevention to meet your complex fintech requirements.Fintech-Specific Security Knowledge
Hire our FlutterFlow fintech developers who precisely comprehend where financial apps get hacked; hence, they ensure adherence to the following:- PSD2 SCA Compliance that is incorporated seamlessly into MFA flows
- Behavioral fraud detection that is layered atop standard authentication
- Secure key management for PCI DSS compliance
Seamless MFA & Biometric Integration
We do not believe in clunky authentication experiences. Our FlutterFlow Fintech developers combine:- TOTP (Google Authenticator) for high-risk actions.
- Face ID/Fingerprint for frictionless logins.
- Fallback protocols so that users are not locked out.
// Biometric auth integration in FlutterFlow
LocalAuth.authenticate(
biometricOnly: true,
stickyAuth: true, // Prevents iOS backgrounding issues
);
Ongoing Security Audits and Maintenance
The amazing part is that fintech threats and their defenses keep evolving. Hence, our experienced FlutterFlow fintech developers follow these practices:- Quarterly penetration tests with a focus on auth endpoints
- Automated monitoring for anomalous logins like brute-force attacks and failed MFA attempts.
- Dependency updates to patch Firebase/FlutterFlow vulnerabilities
Regulatory Compliance Assurance
Our developers do not merely check boxes; they build compliance into the architecture by incorporating:- GDPR/CCPA for proper data handling in auth flows
- Open Banking-ready APIs with fine-grained permissions
- Audit trails for every authentication event, like who logged in, from where, and when.
Work With FlutterFlow Experts Who Prioritize Fintech Security
Hire our team to implement enterprise-grade authentication that meets standards.



