HIPAA Compliance Rules and Requirements

1. What is Protected Health Information in HIPAA?
The subject matter of HIPAA is Protected Health Information or PHI. The main purpose of the act is to protect PHI. PHI of patients includes their personal details like contact numbers and addresses as well as their medical records.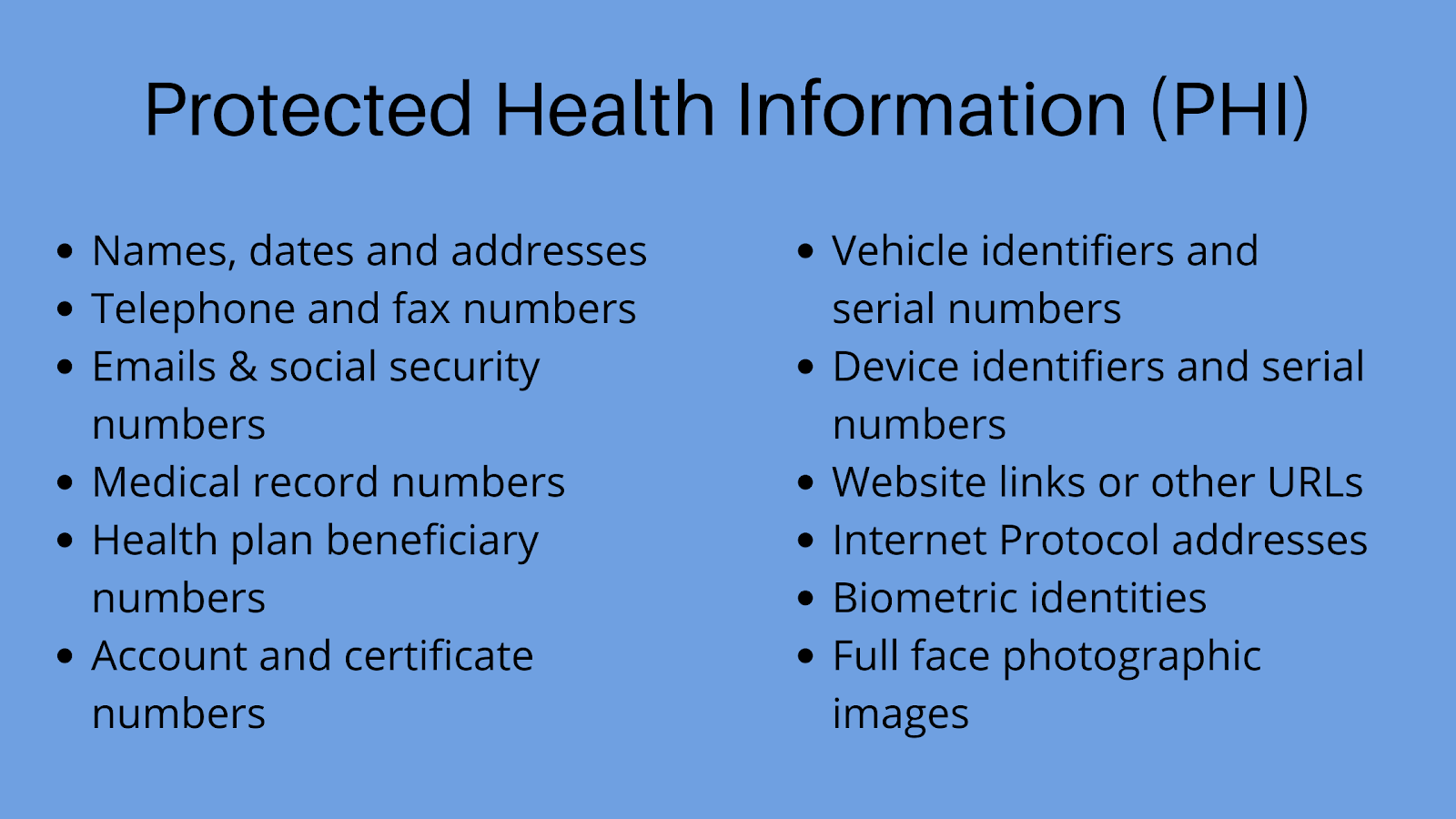
2. Who are the covered entities according to the HIPAA Act?
A covered entity is anyone who works in the healthcare industry and/or can access PHI. In that sense, hospital admin staff, medical staff, or insurance agents, can be covered entities under the HIPAA.3. Who are Business Associates under the HIPAA Act?
Business associates are those who do not work in the medical field directly but closely function with the covered entities. Examples include IT specialists and lawyers. Since they collaborate with medical institutions, they also have access to the PHI. The complete HIPAA compliance checklist for software development is majorly useful to this category of stakeholders.HIPAA Compliance Rules For Software Development
1. The HIPAA Privacy Rule
As per the latest update, the HIPAA Privacy Rule constitutes the requirements regarding PHI protection. Therefore, clinical history, payments for healthcare treatment, and any other medical information must be secure and inaccessible to third-parties.Additionally, the rule describes those certain situations under which certain people can access PHI without patient authorization. It also defines the limitations and rights of the patients. Under this rule, the patients can examine their personal medical records and request copies of the same. In case of a mismatch or an error, the patients may also request corrections.2. The HIPAA Security Rule
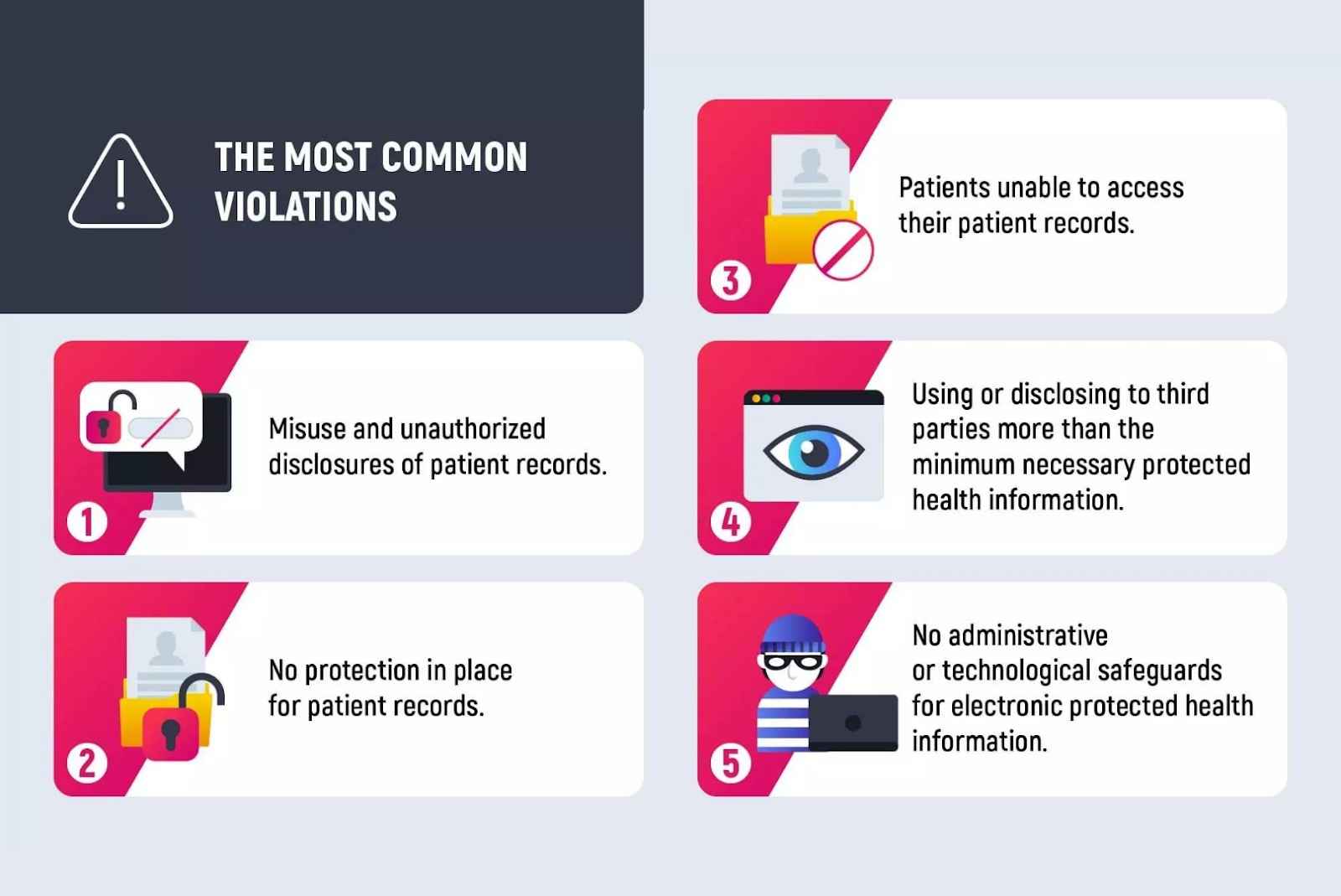
The HIPAA Security Rule lays down conditions for PHI security. It includes specific recommendations and limitations regarding health information security. Essentially, this rule helps in identifying, correcting and preventing future security risks.The rule dictates that the covered entities are required to conduct a periodic data breach risk analysis in order to ascertain reliable PHI protection.3. The HIPAA Enforcement Rule
The HIPAA Enforcement Rule clarifies the investigation provisions and financial penalties in situations of a data breach. However, the penalty amount varies with the number of medical records exposed and the frequency of data breaches in an organization. Generally, a first-time breach can cost an organization from $100 t0 $50,000 but the subsequent breaches can cost as high as $1.5 million.4. The Breach Notification Rule
According to this rule, if the data breach has affected less than 500 individuals, then the organization must send a notification to all those individuals within 60 days of the discovery of the breach. The company must also inform the Office For Civil Rights of the US Health and Human Services within 60 days of the start of a new calendar year. If more than 500 individuals are affected by a data breach then the organization is obliged to notify the media as well.5. The Omnibus Rule
The Omnibus Rule was added in January 2013 and adds to the above-mentioned rules. Typically, this rule extends the obligations of business associates to comply with the HIPAA rules while dealing with PHI.Complete HIPAA Compliance Checklist for Software Development
1. User Authorization
The US government classifies the degree of identity assurance in software applications into four levels. The lowest levels employ only a single-factor authentication. Thus, if a user is able to freely access the system with only a password, the level of security is the lowest. Higher levels make use of multi-factor authentications wherein users need to verify their mobile phones, email addresses, etc. To make your software HIPAA-compliant, you need to include at least two of the below-mentioned factors:Knowledge: A visitor is required to enter a unique data, the knowledge of which is held only by the legit user. Example: PIN or password.Possession: The users are provided with additional data, like security code, by the platform. Thus, the visitor needs to enter that data so as to ensure legal possession of the information.Inherence: A biometric scan is used to verify an inherent characteristic of the user that can't be copied or modified.Location: Allowing access only if the user is located in a particular location at the time of access. A HIPAA-compliant software solution must remember its users. Moreover, it should allow doctors to access patient data without having to follow the complex protocol every time they need vital information.2. Remediation Plan
The remediation plan is a security plan that details the measures taken by the business associates for patient data protection. So it documents safety best practices, including the following aspects:- A list of all the tasks that will be undertaken to ensure data security
- Clear identification of each team member’s responsibility for the same
- Plan of action to overcome challenges in future
3. Emergency Mode
An emergency mode plan guides an organization's plan of action during an attack. It specifies the methods, tasks, and practices to keep the records of the patients safe during an emergency. Therefore, this emergency plan of your HIPAA compliant healthcare app must contain the following information:- A complete list of all the team members along with their roles, contact, and responsibilities.
- Details of all the digital healthcare systems that the organization uses
- A step-by-step procedure for implementing the plan (how, when, by whom)
- Recovery procedures