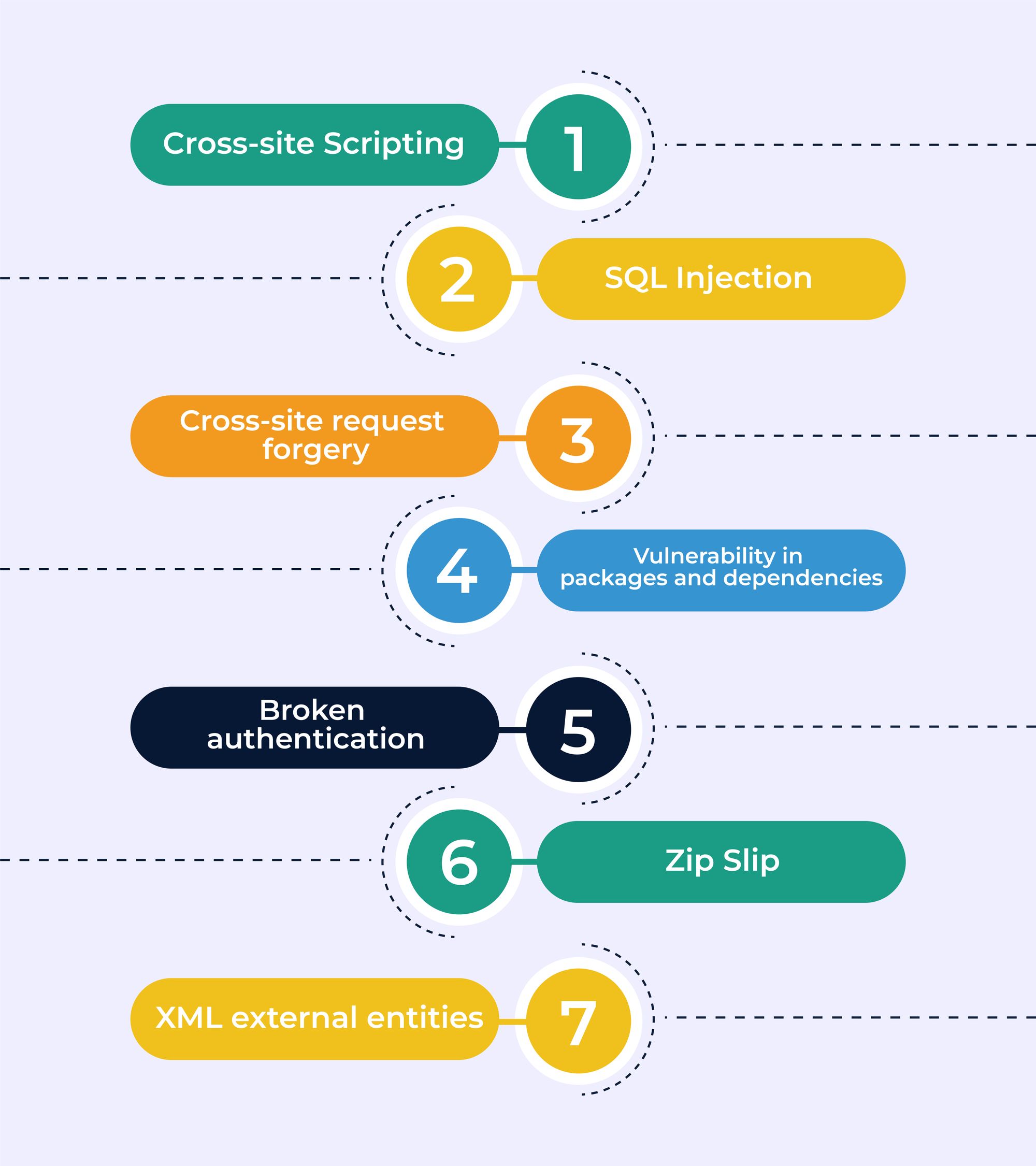
Blog Summary: It is crucial to be well aware about the top React security vulnerabilities to avoid them beforehand. To guide you through the right path, in this blog we will discuss the top 7 serious React security vulnerabilities and how to avoid them including -
✅Cross-site scripting
✅SQL injection
✅Cross-site request forgery
✅Vulnerability in packages and dependencies
✅Broken authentication
✅Zip slip
✅XML external entities
React is a highly sought-after front-end framework for building efficient web applications, both single-page (SPAs) and multi-page (MPAs). While it offers numerous benefits, React can also expose security vulnerabilities if not handled correctly.

It's essential to understand and address these potential risks by following React security best practices. By doing so, you can ensure the protection of your web application against potential threats, figure out how to find React memory leak, or reduce create-react-app vulnerabilities and enhance its overall security.
Despite its many benefits, React can also be vulnerable to security threats. As with any technology, it's crucial to be aware of and address these potential vulnerabilities. Here, we will explore the common security challenges faced by React applications and the React security best practices to ensure their security.
React Security: Common Vulnerabilities & How to Address Them
There are many minor vulnerabilities that we aren’t covering here because it’s basic stuff. So here are the top 7 React security vulnerabilities serious enough to break your application and how to prevent them:
1. Cross-Site Scripting (XSS)
Securing a React application is crucial to prevent potential security vulnerabilities that can compromise the integrity of your web app. Cross-site scripting (XSS) is one of the most common React security vulnerabilities that your web app may face.
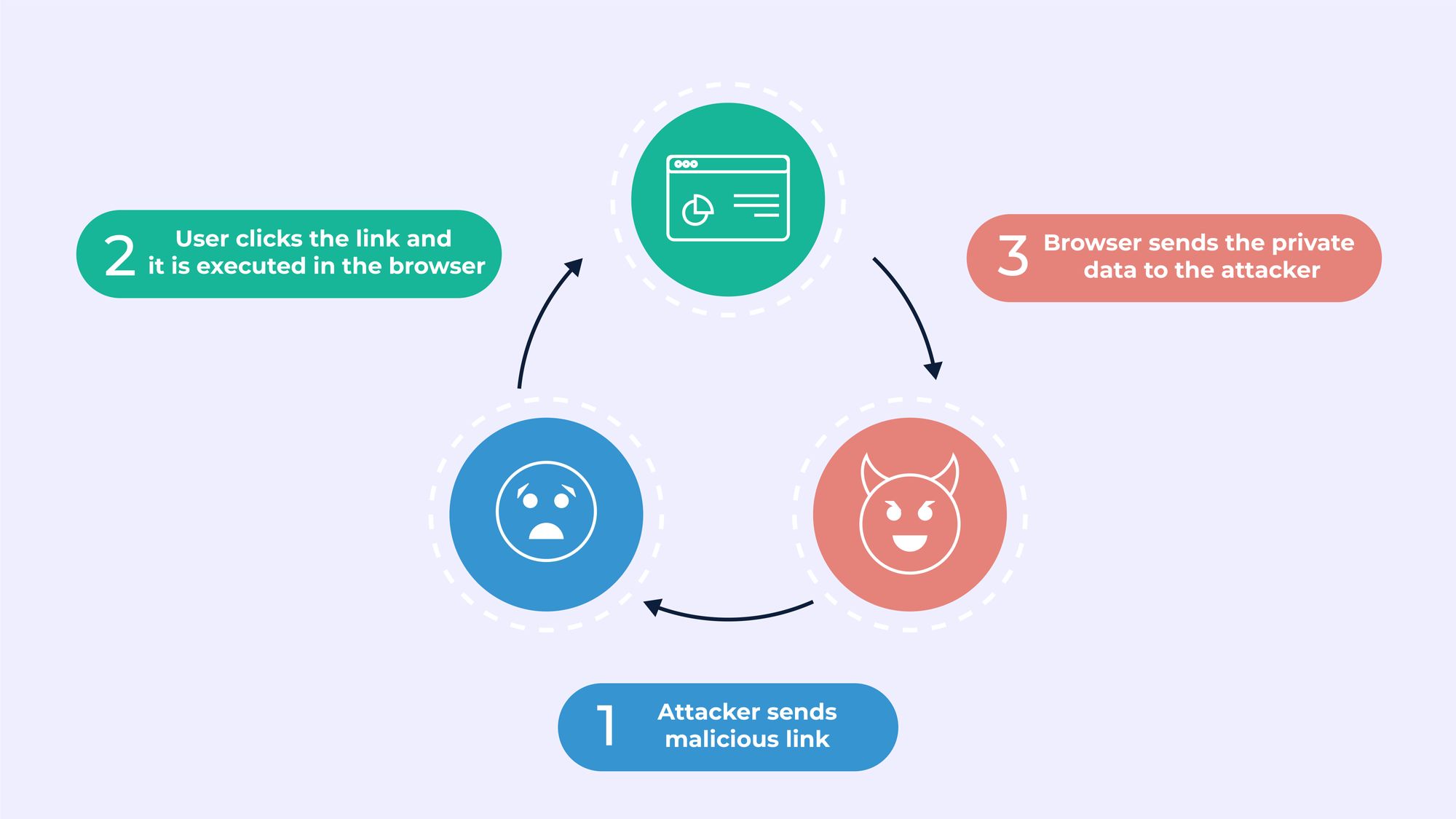
XSS attacks occur when malicious client-side scripts are injected into web pages, which users may click or accept, leading to -
👉Compromised access controls
👉Stolen sessions or cookies
👉Unauthorized connections to computer cameras or ports

There are two types of XSS attacks that a web application may encounter:
✅Reflected Cross-Site Scripting: Reflected XSS occurs when an attacker uses a malicious link with misinformation that gets into the page and is read by the browser as app code.
✅Stored Cross-Site Scripting: Stored XSS occurs when an attacker uploads malicious content, such as unwanted images or comments, with the aim of having it rendered on an application page.
How to prevent cross-site scripting?
By following these React security best practices, you can ensure the security and protection of your web app against XSS attacks and other potential React security vulnerabilities.
- Disabling markups with code running instructions, such as elements like <object>, <script>, <link>, and <embed>, is an effective way to prevent XSS security vulnerabilities in React applications.
- Using {} for default data binding is another defense against XSS. The React framework will escape values automatically when you do this, but it only works with textContent and not with HTML attributes.
- Implementing WAF (Web Application Firewall) in your code can help protect against XSS attacks with its signature-based filtering.
- An HTML library that can parse HTML formatted-text can easily sanitize your HTML markup against XSS vulnerabilities. OWASP offers libraries like OWASP Java HTML Sanitizer and HtmlSanitizer for this purpose.
- URL parsing and Whitelist/Blacklist validation can also be helpful in avoiding XSS attacks on a React application.
See More:- React 19: What’s New, Latest Features, and Updates
2. SQL Injection
SQL injection (SQLi) is a common security vulnerability that can compromise the integrity of data in React applications. Hackers can inject malicious SQL code into your database, enabling them to receive, edit, or delete data without being restricted by user permissions.
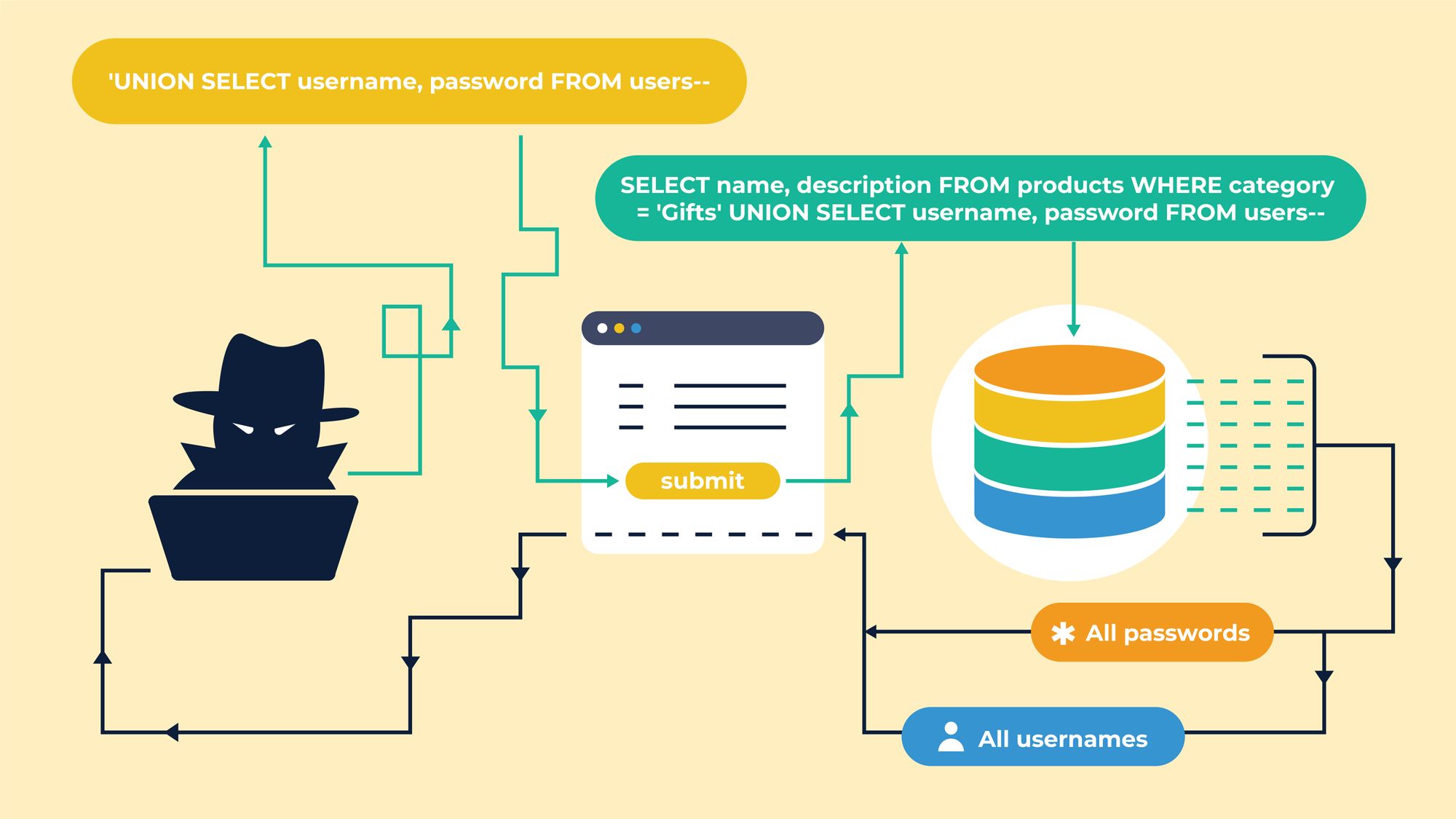
This type of security attack can cause significant harm to an organization's systems, as hackers can modify or destroy sensitive data. SQL injection can occur due to a variety of reasons, including -
👉Improper coding
👉Weak security controls
👉Lack of user input validation
Looking for the right software development company to partner with?
With over more than 10 years of experience in software development, we, at Third Rock Techkno, offer a broad range of software development services and solutions. Our expert professionals not only ensure timely project completion and product launch within budget, but also help your product find the right market positioning and help you grow to meet your business goals.
Get in touch with us for free consultation!
How to prevent SQL injection in React?
To prevent SQL injection in React applications, you need to adopt the below-mentioned React security best practices.
- Filtering all user inputs through a strict whitelist to protect against SQLi, as it ensures that all inputs are thoroughly vetted before being processed.
- Following the principle of least privilege by assigning only the necessary privileges to different accounts. For instance, when a website needs to extract content using SELECT statements, it should only have that privilege, and not have access to privileges like UPDATE, INSERT, or DELETE.
- Using vulnerability scanners, such as Acunetix, to periodically scan your React applications can help identify and address any security weaknesses before they are exploited by attackers.
- Validating all API functions with respect to their API schemas, especially to avoid time-based SQLi.
Additionally, organizations should prioritize implementing secure coding practices, such as following the secure product development lifecycle, and performing regular security scans, testing, and code review. By following these best practices, React applications can be secured against the dangers of SQL injection and other security vulnerabilities.
See More: Hiring a React Developer: React Developer Salary, Skills and More
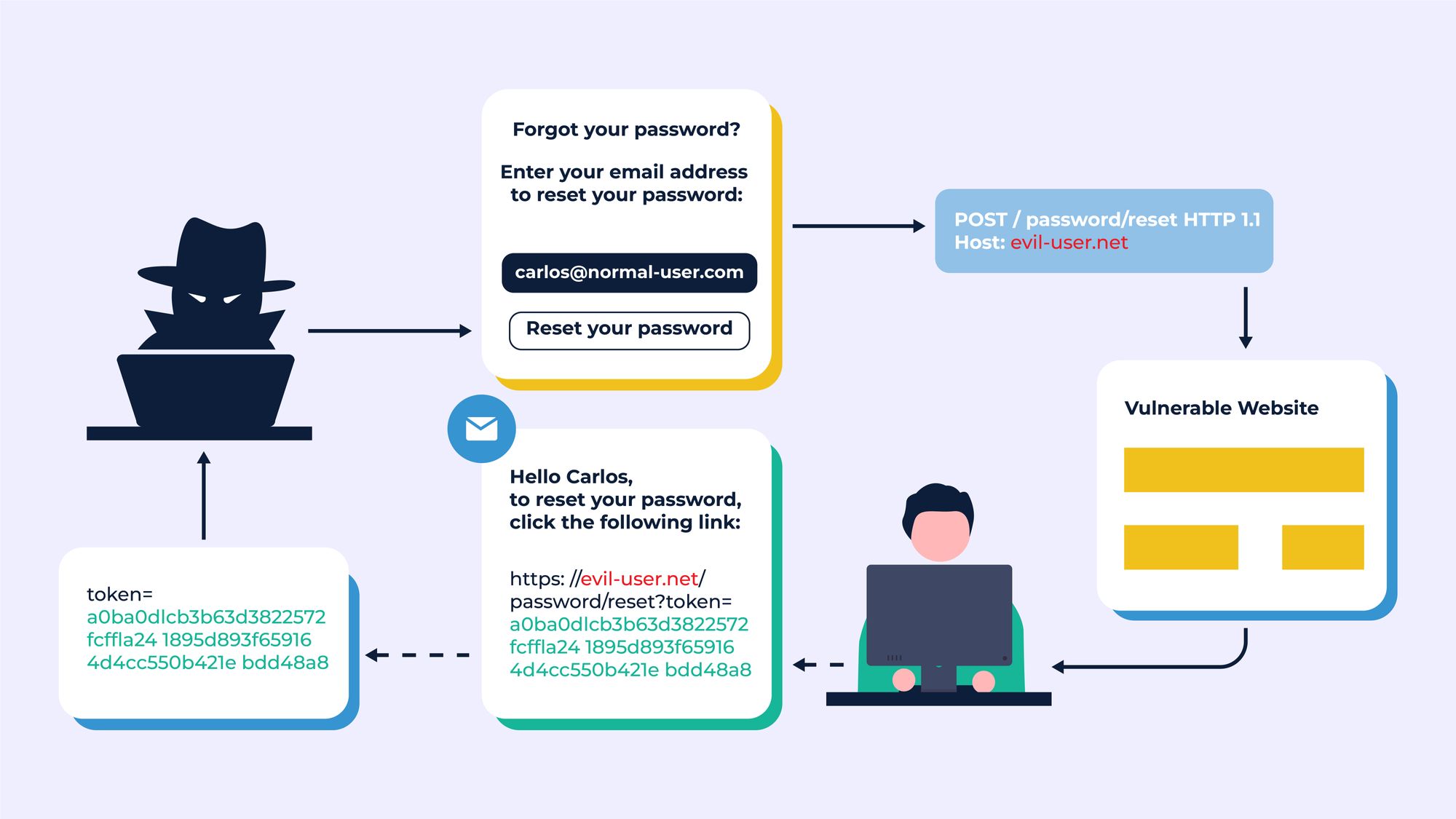
3. Cross-site Request Forgery
Cross-Site Request Forgery (CSRF) is a security vulnerability that affects many websites and web applications, including those built with React. CSRF attacks -
👉Exploit the trust a website has in a user's browser
👉Tricks the user into making unwanted requests to the server.
These requests can range from simple GET requests to dangerous POST requests that can modify or delete data.
How to prevent cross-site request forgery in React?
React, like many other front-end frameworks, is vulnerable to CSRF attacks if proper security measures are not taken. However, the proper React security best practices can help you prevent these attacks such as -
- Implementing a server-side protection mechanism by generating a unique token for each user session and including it in the header of all requests. The server can then validate the token before processing the request, ensuring that only requests originating from your application are accepted.
- Using the "same-site" cookie attribute which tells the browser to only send the cookie with requests made to the same domain as the cookie. By setting this attribute, you can prevent the browser from sending your cookie to an attacker's website, even if the user has been tricked into clicking a link.
In addition, React offers several libraries and packages that can help you secure your application against CSRF attacks. One such library is the csurf library for Express, which provides easy-to-use middleware for protecting your application against CSRF attacks.
When building React applications, it's important to keep in mind that front-end security is just as important as server-side security. By implementing these best practices, you can help protect your users and your data from malicious actors.
It's also crucial to keep your React and npm packages up to date, as new security vulnerabilities are discovered and patched on a regular basis. Staying informed about react security vulnerabilities and subscribing to security mailing lists can help you stay on top of any new threats.
4. Vulnerability in Packages and Dependencies
Vulnerabilities in packages and dependencies refer to security weaknesses or holes in the code of these software components that can be exploited by attackers to gain unauthorized access or cause damage to systems.
These vulnerabilities can arise due to a variety of reasons, such as -
👉Outdated software components
👉Coding errors
👉Insufficient testing
👉Lack of proper security controls
In many cases, these vulnerabilities remain unnoticed for an extended period, allowing attackers to exploit them and compromise the security of systems that rely on the affected packages or dependencies.
How to avoid vulnerability in packages and dependencies in React?
To avoid vulnerabilities in packages and dependencies, it is important to adopt a proactive approach that involves regular security scans, testing, and monitoring. Here are some of the top React security best practices to help you with that.
- Keeping software components up-to-date to ensure that any known vulnerabilities are promptly addressed. Additionally, organizations should implement security controls, such as access controls, firewalls, and encryption, to reduce the risk of exploitation.
- Regularly reviewing the code of packages and dependencies to identify and address any potential security weaknesses. It is also recommended to use verified and trusted sources for downloading and updating packages and dependencies, and to thoroughly vet the code before using it.
- Adopting a robust software development lifecycle (SDLC) that includes security as a critical aspect and involves regular security testing and code review.
5. Broken Authentication
Broken Authentication is a significant security vulnerability that can affect all web applications, including React apps. Poorly implemented session management functions and authentication processes can be easily exploited by hackers to bypass or compromise the authentication solutions put in place in the app.
This vulnerability can lead to the manipulation of user account information, passwords, session tokens, and more.
The leading cause behind broken authentication is often the improper implementation of access and identity controls. Some common security risk factors in React related to broken authentication include -
👉Predictable or easily guessable login credentials
👉Unprotected user authentication credentials
👉Session IDs exposed in the URL
👉Vulnerable session IDs susceptible to session fixation attacks
👉Session values that do not time out or get invalidated after logout
👉Session IDs that are not rotated after a successful login
👉Credentials such as passwords, session IDs, and others sent over unencrypted connections
How to avoid broken authentication in React?
To avoid broken authentication, it is essential to follow these best practices for React security.
- Employing multi-factor authentication wherever possible
- Enforcing password checks for strength
- Using NIST 800-63 B guidelines for password length and complexity
- Using consistent messages for all authentication-related outcomes
- Utilizing a secure, server-side session manager to generate a new session ID each time a user logs in.
Additionally, it is crucial to store session IDs securely and to invalidate them after the session ends to ensure that the app remains secure.
See More: How to Integrate GraphQL with React Web Application
6. Zip Slip
Zip slip is a security vulnerability in React apps that let users submit zip files. Web developers enable this feature to reduce file sizes while they are being uploaded. The app then decompresses these files to retrieve the original files in the zip. Zip slip is basically a directory traversal that hackers can exploit to extract files, most commonly from an archive.
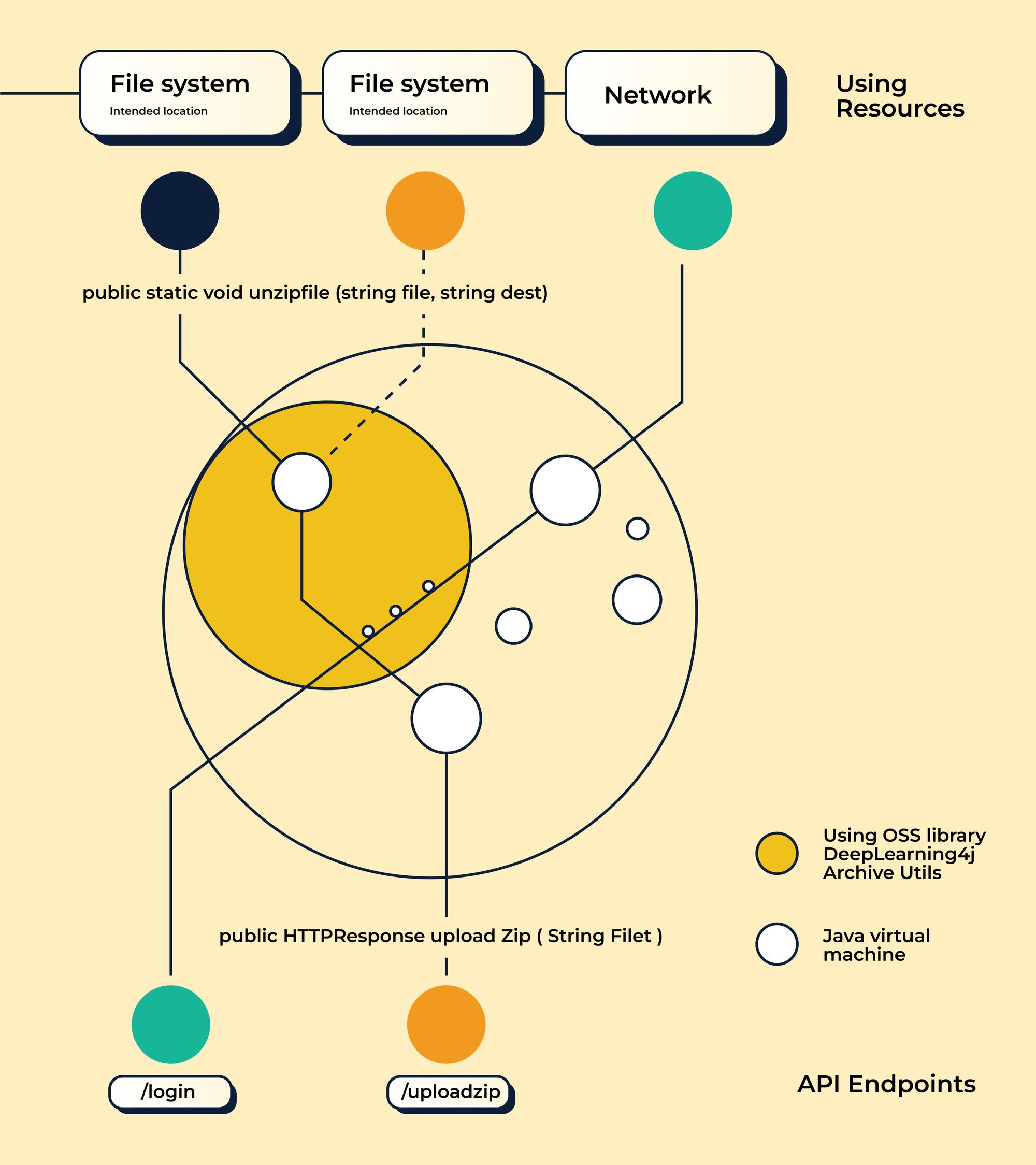
Sometimes, a few parts of a file system can remain outside their designated folder. The attacker may -
👉Gain access to these file parts
👉Overwrite them
👉Invoke these files remotely or make the system to call them
In this way, they manage to achieve Remote Command Execution on the user’s device.
You have to be extra cautious about this React security vulnerability. It can lead to overwriting of sensitive resources like configuration files. What’s worse? The attacker can exploit this not only on the client-side but also on the server-side.
How to avoid zip slip in React?
The only way to avoid this security pitfall is to ensure no malicious file enters the application. The following are the React security best practices for preventing zip slip in React:
- Ensuring the files are named with standard names
- Not allowing special characters in file names
- Always comparing and matching the names with regular, standard expressions
- Renaming all the uploaded files in a zip and generating new names for each one before the app uses or stores them.
7. XML External Entities (XXE)
In certain cases, XXE attacks are also considered a type of injection attack. XML parsers that are outdated in your React web application become the most vulnerable to get abused with injection attacks leading to DoS attacks. In such attacks -
👉The perpetrator attempts to collect confidential data from the server
👉In certain cases, XXE attacks fall under the category of injection attacks
👉Outdated XML parsers in your React web app are the most vulnerable to injection attacks that lead to DoS attacks
👉The attacker aims to collect sensitive data from the application server
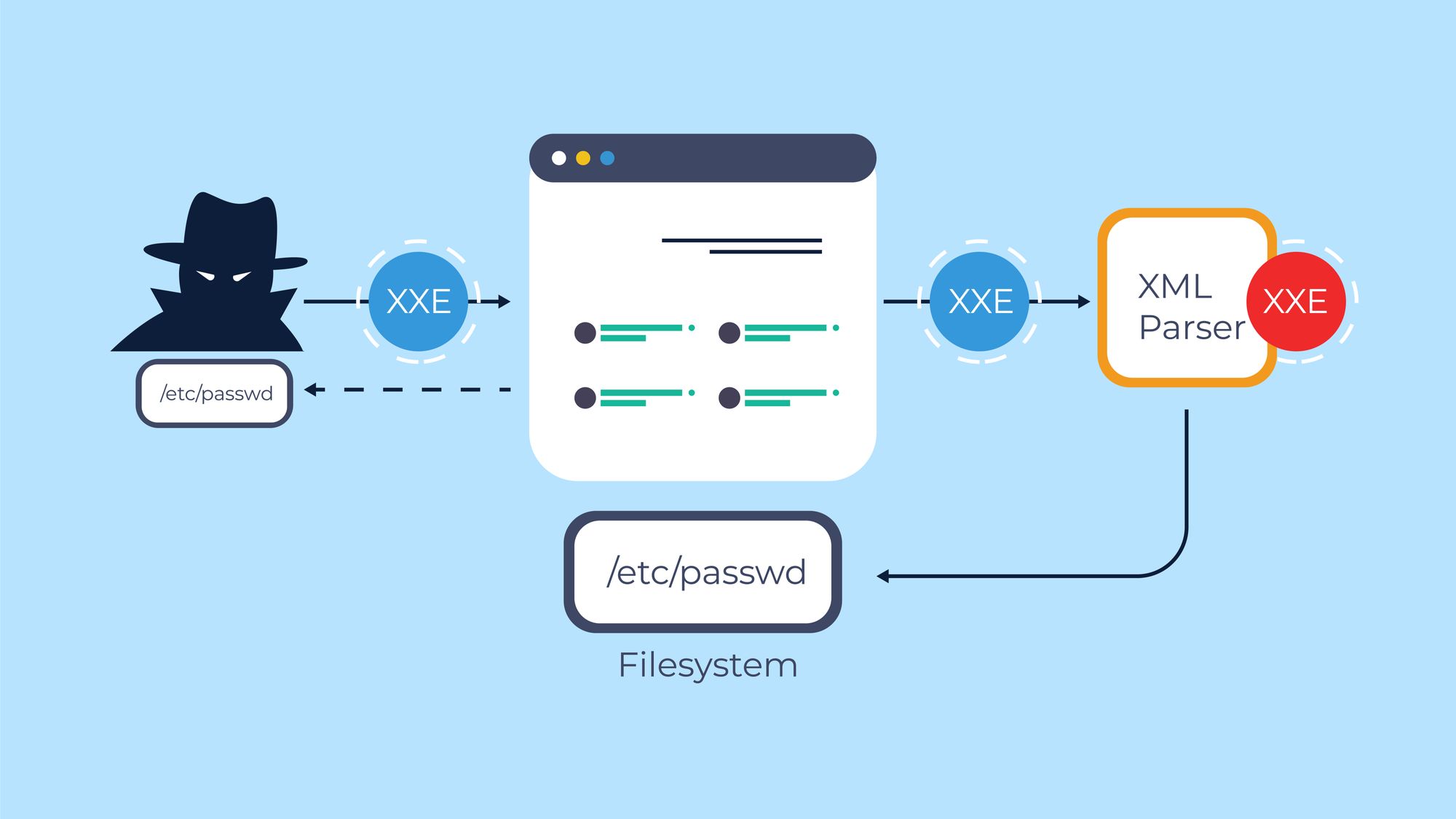
How to avoid XXE security attacks in React applications?
Below are the React security best practices to avoid XXE security attacks in React applications -
- Not serializing sensitive data. You can use complex JSON formats to avoid serialization. Some SAST tools may prove helpful in identifying malicious XXE in your code. You can use them to secure your React app.
- Upgrading the XML processors regularly as this security pitfall arises because of outdated XML processors.
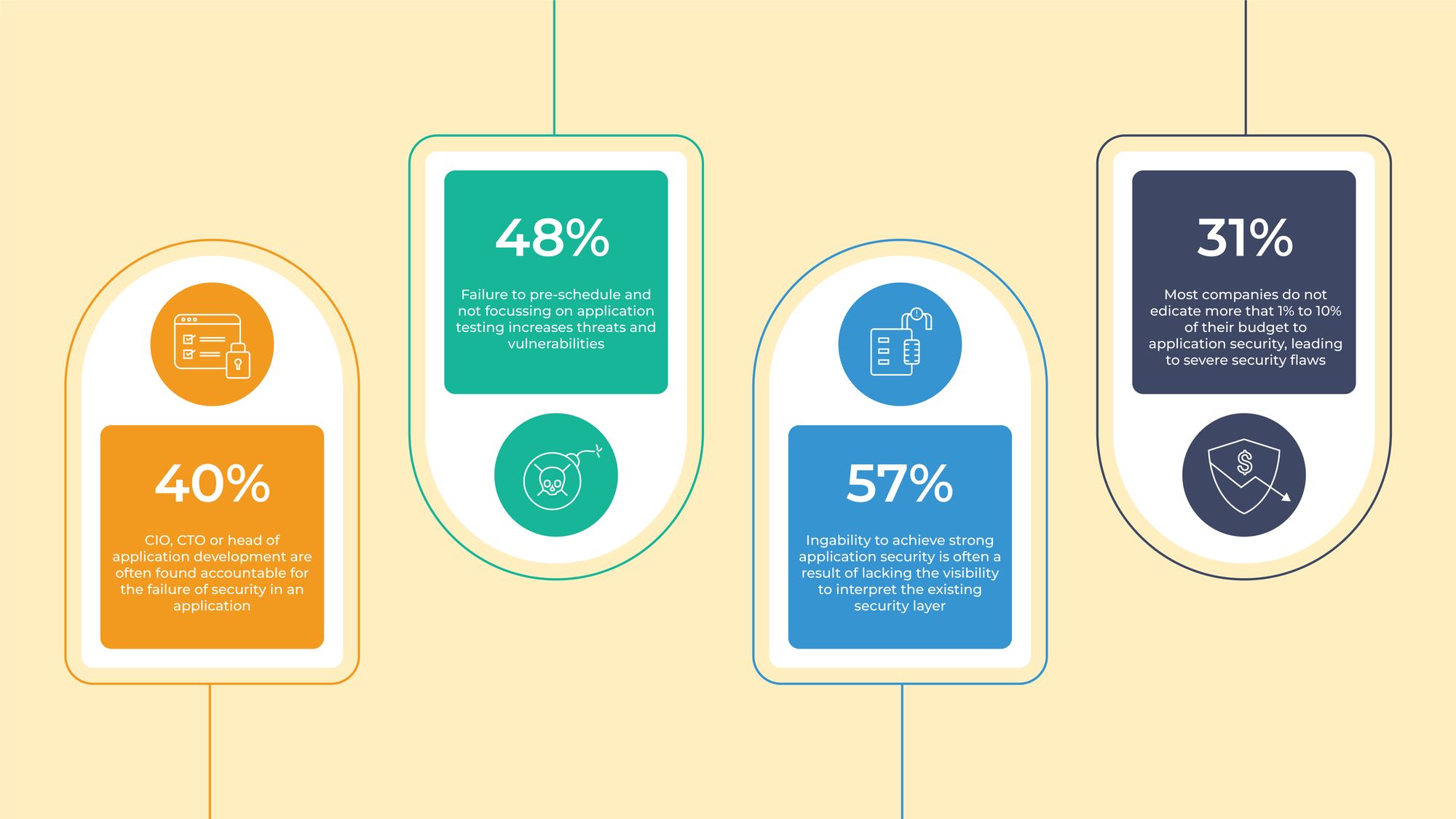
React Security Best Practices Followed by Third Rock Techkno
At Third Rock Techkno, we are acutely aware of the importance of application security, both for businesses and users alike. The challenge in the React world is the lag between reporting security issues and deploying a solution, with every new release of React presenting one or more security challenges to the community.
That's why at Third Rock Techkno, we have adopted a proactive development methodology that ensures security checks and testing for vulnerabilities at every stage of the React web app development process. Our team of over 100 skilled developers and QA testers keep themselves informed on the latest security trends, including React security best practices for multi-page and single-page applications.
Our approach to securing React apps is comprehensive and includes measures such as -
- 360-degree data validation
- End-to-end encryption
- Multi-factor authentication,
- 24x7 DNS protection to prevent attacks such as XSS and XXE.
By following the latest security trends and best practices in React, we can ensure that our clients' web apps are as secure as possible.
Take a look at our extensive portfolio and drop us a line to get started today.
FAQs
1.What are React security vulnerabilities?
React security vulnerabilities are weaknesses in the code of a React web application that can be exploited by malicious actors to compromise sensitive information or harm the functionality of the app.
2.Why are React security vulnerabilities serious enough to break an application?
React security vulnerabilities, if left unaddressed, can cause severe damage to the user data and reputation of the business. Hackers can exploit these weaknesses to steal sensitive information, manipulate user data, and even shut down the entire application.
3.What are some common React security vulnerabilities?
Some of the most common React security vulnerabilities include cross-site scripting (XSS), cross-site request forgery (CSRF), SQL injection, broken authentication, and unauthorized access.
4. How can React security vulnerabilities be prevented?
React security vulnerabilities can be prevented by implementing security best practices such as data validation, multi-factor authentication, encryption, and regularly scanning the application for any potential vulnerabilities. Regular software updates and educating developers about security risks can also help in avoiding React security vulnerabilities.


